1. Introduction
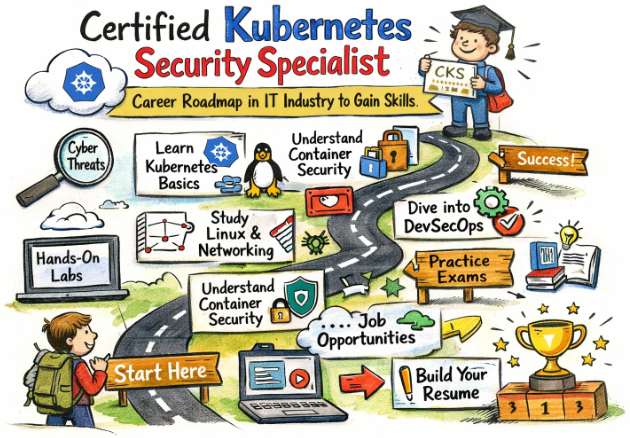
The security of containerized environments is no longer an optional task; it has become a fundamental requirement for every modern organization. As Kubernetes has been adopted as the primary choice for cloud-native orchestration, a significant increase in the demand for specialized security expertise has been observed. In this comprehensive guide, the Certified Kubernetes Security Specialist (CKS) certification is explored in great detail. A clear roadmap is provided for engineers and managers to understand the learning path, the practical applications, and the long-term career outcomes associated with this prestigious credential.
In the current landscape of software development, the rapid migration to the cloud has introduced new layers of complexity. While Kubernetes provides incredible scaling and management capabilities, the underlying infrastructure is often left exposed if security is not prioritized from the very beginning. The Certified Kubernetes Security Specialist (CKS) has been established as a critical benchmark for identifying professionals who can navigate these security challenges effectively.
What is Certified Kubernetes Security Specialist (CKS)?
The CKS is recognized as a performance-based certification that validates an individual’s competency in securing container-based applications. Unlike traditional exams that rely on multiple-choice questions, the CKS requires the candidate to solve real-world security problems within a live Kubernetes environment using a command-line interface. A broad range of skills is tested, including the ability to secure the container supply chain, harden the cluster, and monitor for threats during runtime.
Why it matters in today’s software, cloud, and automation ecosystem
The ecosystem of today is built on the pillars of speed and automation. When CI/CD pipelines are utilized to push code multiple times a day, a single security misconfiguration can be magnified across the entire infrastructure. The CKS is designed to address these risks by ensuring that security best practices are integrated into the deployment lifecycle. A “shift-left” approach is encouraged, where security is considered at the build stage rather than being added as a final, often incomplete, step.
Why certifications are important for engineers and managers
For engineers, certifications like the CKS serve as an objective measure of technical skill. In a competitive job market, a performance-based credential provides immediate proof of expertise that a resume alone might not convey. For engineering managers, these certifications are vital for team building and risk management. When a team is composed of certified specialists, a higher standard of operational security is maintained, and the likelihood of costly security breaches is significantly reduced.
Why Choose DevOpsSchool?
When a journey toward advanced certification is started, the selection of a training partner is a decision of great importance. DevOpsSchool is highly regarded in the industry for providing a learning environment that is both structured and practical.
- Curriculum Depth: The training modules are meticulously designed to cover every aspect of the official exam syllabus, ensuring that no topic is left unexplored.
- Expert Instruction: Guidance is provided by instructors who possess extensive experience in real-world production environments.
- Hands-on Labs: A significant portion of the training is dedicated to practical exercises, which is essential for a performance-based exam like the CKS.
- Continuous Updates: As the Kubernetes ecosystem evolves, the course content is regularly updated to reflect the latest security tools and best practices.
- Resource Library: A vast collection of study materials, recorded sessions, and practice exams is made available to every learner.
Certification Deep-Dive
What is this certification?
The Certified Kubernetes Security Specialist (CKS) is an advanced-level credential that focuses on the security of the entire Kubernetes ecosystem. It is designed to test the ability to protect clusters from the moment they are provisioned through their entire operational life.
Who should take this certification?
This certification is intended for professionals who have already attained the Certified Kubernetes Administrator (CKA) status. It is ideally suited for Security Engineers, Cloud Architects, and DevOps professionals who are responsible for maintaining the integrity of production workloads.
Certification Overview Table
| Track | Level | Who it’s for | Prerequisites | Skills Covered | Recommended Order |
| DevOps | Intermediate | Platform Engineers | Linux Basics | CI/CD, Automation | Start with CKA |
| DevSecOps | Advanced | Security Analysts | CKA Certification | Hardening, Scanning | Follow CKA with CKS |
| SRE | Advanced | Reliability Engineers | CKA/CKS | Observability, Stability | Post-CKS |
| AIOps | Advanced | ML Engineers | Data Science | Model Automation | Post-MLOps |
| DataOps | Intermediate | Data Engineers | SQL/Python | Pipeline Security | Mid-Level |
| FinOps | Intermediate | Financial Managers | Cloud Economics | Cost Governance | Cross-Track |
Skills you will gain
Through the preparation for the CKS, a wide array of technical skills will be mastered:
- Cluster Hardening: Knowledge is gained on how to restrict access to the API server and secure the etcd database.
- System Security: Techniques for reducing the attack surface of the host operating system are learned.
- Microservice Isolation: The implementation of Network Policies is mastered to control traffic flow between pods.
- Supply Chain Protection: The ability to verify image signatures and scan for vulnerabilities is developed.
- Runtime Monitoring: Tools are utilized to detect unauthorized access and suspicious behavior in real-time.
Real-world projects you should be able to do after this certification
Upon successful completion of the certification, several complex projects can be managed:
- A comprehensive security audit of an existing Kubernetes cluster can be performed.
- An automated image scanning gate can be implemented within a Jenkins or GitLab pipeline.
- A Zero-Trust network architecture can be designed using Kubernetes Network Policies.
- Runtime threat detection systems can be deployed to monitor high-stakes production applications.
- Secure secrets management solutions can be integrated with external vaults.
Preparation plan
7–14 Days Plan
- The official exam curriculum is reviewed in detail to identify knowledge gaps.
- High-weightage areas such as Cluster Hardening and Runtime Security are prioritized.
- Kubernetes documentation is practiced daily to ensure quick navigation during the exam.
- A simulated environment is used to solve at least two full mock exams.
30 Days Plan
- The first two weeks are spent deeply exploring Linux security modules and container fundamentals.
- The third week is dedicated to mastering third-party security tools like Falco and Trivy.
- The final week is used for intense lab practice, focusing on speed and accuracy in command execution.
60 Days Plan
- A slow and steady approach is taken to master every sub-topic, including AppArmor and Seccomp profiles.
- Extensive research into the latest Kubernetes security whitepapers is conducted to understand the “why” behind the “how.”
- Multiple real-world scenarios are built from scratch to test various security configurations.
Common mistakes to avoid
- Over-reliance on Memory: Because the exam is practical, memorizing commands is less effective than understanding the logic.
- Poor Time Management: Spending too much time on a single difficult task can prevent the completion of simpler, high-scoring questions.
- Ignoring the CKA Prerequisite: If the fundamental administration skills are weak, the advanced security tasks will be much harder to complete.
- Not using Documentation: The official documentation is a permitted resource; failing to use it effectively is a common reason for failure.
Best next certification after this
- Same Track: Specialized cloud provider security certifications (such as AWS Certified Security Specialty).
- Cross-Track: Certified Kubernetes Application Developer (CKAD) to understand the developer’s perspective.
- Leadership / Management: CISM (Certified Information Security Manager) for those moving into strategic roles.
Choose Your Learning Path
DevOps Path
This path is chosen by those who want to build the foundation of automated infrastructure. The CKS is added to this path to ensure that the infrastructure being built is inherently secure.
DevSecOps Path
This is the most direct path for security-focused individuals. Every tool and process is viewed through a security lens, and the CKS serves as the core technical credential for this specialization.
Site Reliability Engineering (SRE) Path
For the SRE, a secure cluster is a reliable cluster. This path focuses on using security configurations to prevent outages caused by configuration drift or external attacks.
AIOps / MLOps Path
As AI models are deployed at scale, the infrastructure hosting them must be protected. This path integrates Kubernetes security into the lifecycle of machine learning operations.
DataOps Path
The protection of data integrity is the primary focus here. The CKS provides the tools needed to secure the platforms that process and store massive datasets.
FinOps Path
Cost management is the goal, but security breaches represent a massive financial risk. This path combines cost-saving measures with the risk-mitigation strategies learned in the CKS.
Role → Recommended Certifications Mapping
| Role | Recommended Certification | Importance |
| DevOps Engineer | CKA + CKS | Essential |
| SRE | CKS + Observability | High |
| Platform Engineer | CKS + Cloud Architect | Essential |
| Cloud Engineer | Provider Security + CKS | High |
| Security Engineer | CKS + CISSP | Critical |
| Data Engineer | CKS + Data Professional | Medium |
| FinOps Practitioner | FinOps + CKS (Overview) | Medium |
| Engineering Manager | CKS + CISM | Strategic |
Next Certifications to Take
- For the DevOps Learner:
- Same-track: CKAD
- Cross-track: Terraform Associate
- Leadership: ITIL Foundation
- For the Security Learner:
- Same-track: Azure Security Engineer
- Cross-track: CKA
- Leadership: CISM
- For the Management Learner:
- Same-track: PMP
- Cross-track: CKS (Technical Overview)
- Leadership: MBA or Executive Leadership
Training & Certification Support Institutions
DevOpsSchool is a premier institution that provides end-to-end support for CKS candidates. A focus is placed on long-term skill development rather than just passing the exam. Both live and self-paced learning options are made available.
Cotocus offers specialized consulting and training services. Expertise is shared with organizations that need to implement secure, high-scale Kubernetes clusters. The training is known for its practical, real-world relevance.
ScmGalaxy acts as a major knowledge hub for the community. A massive repository of technical blogs and troubleshooting guides is maintained to help engineers solve complex problems in their daily work.
BestDevOps focuses on career-oriented training. Learning paths are designed to align with the current requirements of top-tier technology companies, ensuring that students are job-ready.
devsecopsschool.com is a platform dedicated specifically to the intersection of development, security, and operations. Highly specialized courses on security automation are found here.
sreschool.com provides education centered on the principles of reliability. The curriculum is built to help professionals maintain high availability in complex distributed systems.
aiopsschool.com bridges the gap between AI and IT operations. Training is provided on how to use artificial intelligence to enhance operational efficiency.
dataopsschool.com is the destination for those looking to master the art of data pipeline management. The focus is placed on building secure and scalable data architectures.
finopsschool.com specializes in cloud financial management. Guidance is offered on how to balance the need for speed and innovation with the requirement for cost-efficiency.
FAQs Section
General Career FAQs
- What is the difficulty level of the CKS?
It is considered a high-level exam due to its practical nature and the broad range of security tools it covers. - How much time is required for preparation?
A minimum of 40 to 60 hours of dedicated study is typically needed for those already proficient in Kubernetes. - Are there any prerequisites?
A valid CKA certification must be held at the time of the CKS exam. - In what sequence should Kubernetes certs be taken?
The path usually starts with CKA, followed by CKS for security or CKAD for application development. - What is the career value of a CKS?
It often leads to specialized roles in cloud security and senior-level DevOps positions with higher compensation. - Which job roles require a CKS?
Roles such as Security Engineer, Cloud Architect, and DevSecOps Lead often list the CKS as a preferred qualification. - Is the CKS recognized globally?
Yes, it is a vendor-neutral certification that is respected by major organizations around the world. - Does the CKS cover cloud-specific tools?
No, it focuses on the core Kubernetes security features and open-source security tools. - What is the growth potential for a CKS holder?
As cloud security becomes more critical, the demand for these specialists is expected to grow significantly over the next decade. - Can I take the exam from home?
Yes, the exam is conducted online with a remote proctor. - Is Linux knowledge necessary?
A strong understanding of the Linux terminal and system-level security is essential. - How much does the exam cost?
The cost is set by the Linux Foundation and often includes one free retake.
Certified Kubernetes Security Specialist (CKS) Specific FAQs
- Is the CKS exam performance-based?
Yes, it consists of several tasks that must be performed on a live Kubernetes cluster. - What happens if my CKA expires?
If the CKA expires, the CKS cannot be taken until the CKA is renewed. - Which security tools are included in the exam?
Tools such as Falco, Trivy, and Clair are frequently featured in the curriculum. - Are Network Policies heavily tested?
Yes, the ability to restrict traffic between namespaces and pods is a major part of the exam. - How long is the CKS exam?
The candidate is given exactly two hours to complete all the tasks. - What is the passing score?
A score of 67% or higher is required to earn the certification. - Can I use a notepad during the exam?
An internal digital notepad is provided within the exam environment for taking notes. - Is image hardening part of the CKS?
Yes, the exam covers the creation of secure Dockerfiles and the removal of unnecessary privileges from containers.
Testimonials
Advik The deep dive into runtime security provided a new level of confidence in managing production workloads. The practical focus of the training was exactly what was needed.
Sanya Skill improvement was immediate after going through the preparation labs. The ability to articulate security risks to the wider team has been a major career benefit.
Vihaan Real-world application was the highlight of this journey. The techniques learned are now being used to secure the entire CI/CD pipeline at my current firm.
Ananya Career clarity was found after achieving the CKS. It has opened doors to senior DevSecOps roles that were previously out of reach.
Kabir Confidence growth has been the biggest outcome for me. Managing complex Kubernetes clusters no longer feels like a security gamble.
Conclusion
The Certified Kubernetes Security Specialist (CKS) certification is an essential milestone for any professional working in the cloud-native space. As the landscape of threats continues to evolve, the skills validated by this credential will only become more valuable.
By achieving this certification, a powerful message is sent to the industry regarding technical proficiency and a commitment to security. The long-term career benefits are substantial, ranging from increased salary potential to the opportunity to lead critical security initiatives. Strategic learning and a well-planned certification path will ensure that professional growth remains steady in this rapidly changing field.